How to secure and personalise your Drupal website

Have you ever worked for a company that’s been hacked?
If you haven’t, you’re amongst a group of people that are growing smaller by the day. According to its Annual Cyber Threat Report 2020–21, the Australian Cyber Security Centre (ACSC) received more than 67,500 cybercrime reports over the 2020-21 financial year — an increase of nearly 13 per cent from the previous year. Put another way, the Centre extrapolates that this increase in volume equates to one report of a cyber attack every 8 minutes, compared to one every 10 minutes last financial year.
Website security should be a priority for all organisations, but if your site happens to run on the Drupal content management system (CMS), you’re in luck, as Drupal is one of the most secure CMS options out-of-the-box. But since there’s always room to improve, I recently offered a few suggestions for improving the security of Drupal core and its contributed modules in a webinar Sitback conducted with Acquia.
I’ve detailed these recommendations in this article — as well as a few suggestions for personalising your Drupal content — but if you missed the first instalment in this series, take a look at it now for more information on improving Drupal’s SEO performance and accessibility. You can also view the full presentation or download the slides below:
Watch the Video
View the Slides
Why Website Security Matters
In 2021 alone, major cybersecurity breaches included big names like Twitch.tv, LinkedIn, Swinburne University, Facebook, Northern Territory Health, and Transport NSW.
But while some of these incidents have come about through targeted hacking attempts, cybersecurity issues don’t generally target single sites. Instead, malicious actors use perpetually operating systems to continually probe for vulnerabilities that can be exploited across many sites.
Unfortunately, what this means is that you may not know when — or even if — your site has been hacked. And if you determine that your site has been compromised, it can be difficult to fully remove malicious code (or even determine how to restore it from a safe point-in-time backup). That’s why it’s important to be proactive — rather than reactive — when it comes to site security.
When thinking about the different aspects of web security, you can categorise considerations into two separate groups: internal (the elements that are dependent upon your application’s code, such as access permission and input sanitisation) and external (i.e., the infrastructure, servers, and network devices that power your site’s operation).
Let’s look at both internal and external security considerations for sites running on the Drupal CMS.
Internal Security in Drupal
As mentioned earlier, if you’re using Drupal, you’ve already taken an important step towards securing your website, since you’re already using one of the more security-conscious CMS platforms on the market.
Yet, even with the strength of Drupal’s CMS, there are still a few basic actions you’ll want to take to keep your site secure:
- Always keep your Drupal core and contributed modules up-to-date. A monthly review of your status and any pending updates should do the trick. The Upgrade Status Report in your Drupal admin section will provide you with a detailed list of what needs upgrading — pay special attention to anything listed in red, which means it has an available security patch or security-related upgrade.
- Only use contributed modules that have a stable release, and that are covered by Drupal’s security advisory policy. Try to review your permissions once every quarter to be safe.
The Best Drupal Modules for Security
The following are a few of my favourite Drupal modules for security:
- Coder: Coder checks your Drupal code against coding standards and other best practices. It can also fix coding standard violations for you with the phpcbf command from PHP_CodeSniffer.
- Hacked: This module scans the currently installed Drupal core, contributed modules and themes, re-downloads them, and determines if they have been changed. Changes are marked clearly, and if the diff module is installed, Hacked will allow you to see the exact lines that have changed.
- Password Policy: This module allows you to define a set of constraints that must be met before a user password change will be accepted. For example, you might decide to require that all user passwords are subject to an uppercase constraint (with a parameter of 2) and a digit constraint (with a parameter of 4). In this case, a user password will have to have at least two uppercase letters and at least four digits for it to be accepted.
- Login Security: The Login Security module improves the security options in the login operation of a Drupal site. By default, Drupal introduces only basic access control, denying IP access to the full content of the site. With the Login Security module, a site administrator can further restrict access by adding access control features to the site’s login forms — for example, by limiting the number of invalid login attempts before blocking accounts or denying access by IP address, either temporarily or permanently.
- Flood Control: Flood Control provides an interface for hidden flood control variables (e.g. login attempt limiters) and makes it possible for site administrators to remove IP addresses and user IDs from the flood table.
- Automated Logout: Finally, this module gives site administrators the ability to log users out automatically, after a specified time of inactivity. The module is highly customisable and includes the ability to set site policies by role to enforce logout.
Hosting Options for Drupal Sites
Once your Drupal site is secured through modules, you’ll want to look at your hosting. Hosting refers to the space that houses your website on the internet, and there are different types of hosting available:
- Infrastructure-as-a-Service (IaaS) providers are responsible for managing many aspects of the hosting environment including applications, runtime, operating systems (OSs), middleware, and data. Providers also manage the servers, hard drives, networking, virtualisation, and storage used for hosting, while some offer more services beyond the virtualisation layer, such as databases or message queuing.
- Platform-as-a-Service (PaaS) services allow businesses to design and create applications that are built into the PaaS through special software components. These applications, sometimes called middleware, are scalable and highly available as they take on certain cloud characteristics.
From a hosting standpoint, each model offers different advantages and disadvantages. IaaS hosts, for example, offer:
- The most flexible cloud computing model
- Easy-to-automate deployment of storage, networking, servers, and processing power
- Hardware purchasing based on consumption
- Complete control retained over infrastructure by clients
- Resource purchasing on an as-needed basis
- Highly scalable to support fluctuating demand
On the other hand, PaaS hosting solutions offer benefits of their own:
- Simple, cost-effective development and deployment of apps
- Scalable and highly available
- Developers can customise apps without the headache of maintaining the associated software
- Significant reduction in the amount of coding needed
- Ability to automate business processes
- Easy migration to the hybrid model
Choosing a Drupal Hosting Solution
While the choice between IaaS and PaaS hosting solutions is highly individual and should come down to your organisation’s specific needs and requirements, the team at Sitback regularly recommends Acquia hosting for Drupal websites.
Not only does Acquia offer a hosting solution that’s specialised for Drupal, it’s also secure, easy to manage, and performance-optimised, thanks to its complete infrastructure abstraction and available utilities for reducing DevOps effort.
External Security in Drupal
As this article primarily focuses on Drupal, I’m not going to spend as much time on external security as on internal considerations. However, a few quick wins you can easily implement from the external perspective include:
- Ensuring you’re using Web Application Firewalls, such as Cloudflare or Akamai. These services act as the first point of defence for your site. More importantly, they can mitigate the risk of a Distributed Denial of Service (DDoS) attack that could bring your website down.
- Ensuring that you’re using an SSL certificate and that all incoming traffic is redirected from non-HTTP to HTTPS.
- Limiting access to your database, so that it’s not open to all web users. Instead, it should be restricted to only the server hosting the web application.
- Disabling FTP access, as it’s not secure enough.
- Setting up and using an automated deployment process from the code repository directly. That way, access to the server will be restricted and developers won’t need to access it to deploy code updates.
Essentially, your goal when it comes to external security in Drupal should be to try and limit access to your server to the greatest degree possible without compromising internal productivity.
Migrating your Website from Drupal 7 to Drupal 9
One final Drupal security piece to consider is that the team behind Drupal have announced that Drupal 7 will reach its end-of-life in November 2022 — which is less than a year away, as of this writing.
If you’re still on Drupal 7 — regardless of whether or not you have a plan for migration — one way to get around this time crunch is to migrate your D7 site over to Acquia hosting. Acquia is currently offering to extend the end-of-life period and provide any necessary security fixes up to 2025, which will buy you an additional three years to plan and migrate your existing website.
For more information on this offer — or to get started with your migration — get in touch with our team.
Personalisation in Drupal
Once you’ve optimised your Drupal site’s performance, SEO, accessibility, security, and hosting, your next step should be to optimise your content by tailoring it for individual users.
Effectively, personalisation is the process of creating relevant, individualised interactions between two parties in order to enhance the experience of the recipient. You can also think about personalisation this way: it is the act of tailoring an experience or communication to an individual, based on what you’ve learned about them.
The Importance of Personalisation
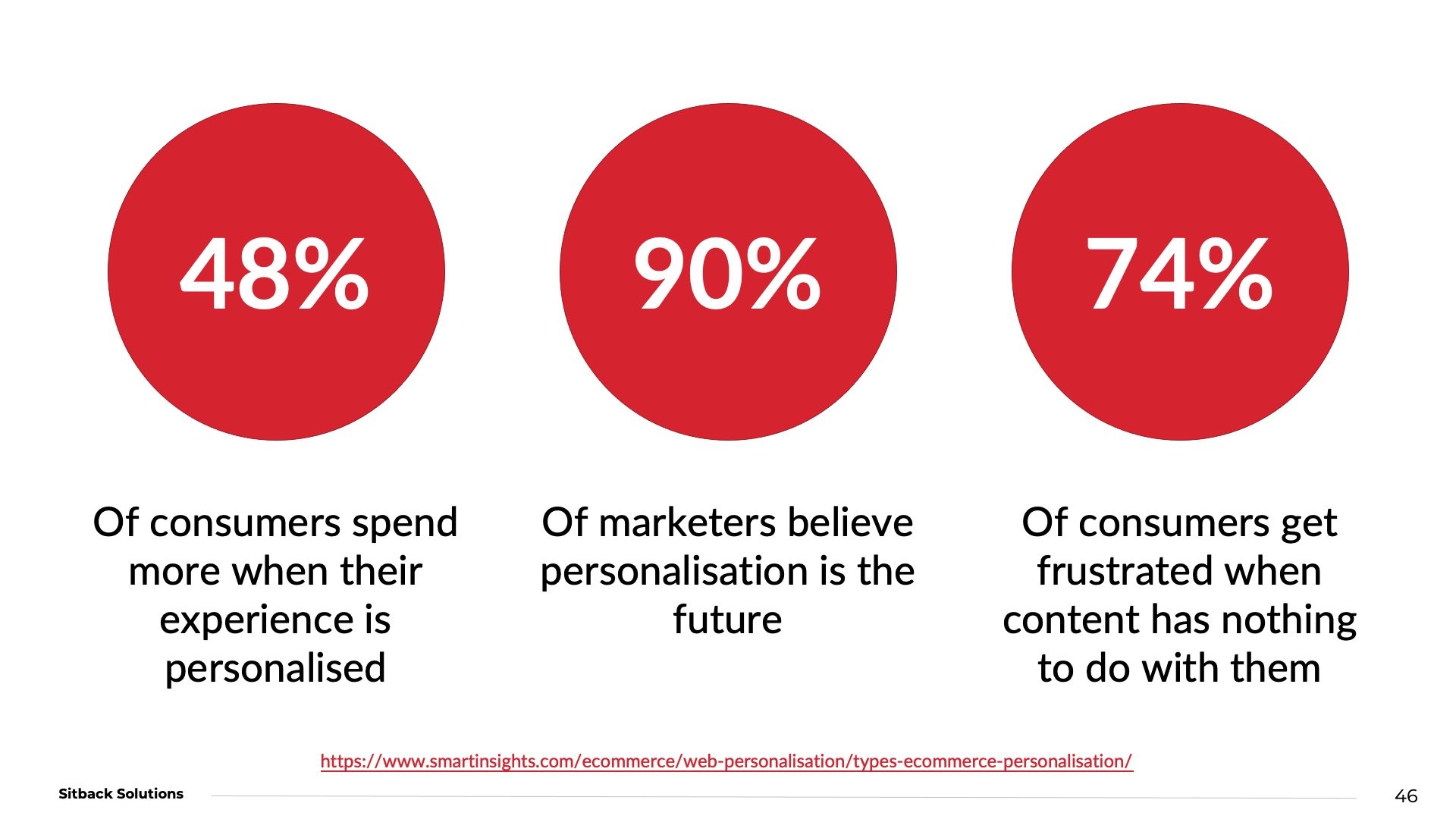
Why should you care about personalisation? The numbers don’t lie:
The importance of personalisation is easier to grasp if you think about your own experiences as a consumer. When you’re on a brand’s website, do you appreciate receiving personalised recommendations and offers? How about content that’s relevant to you, or related to a product or service you’ve recently purchased?
Many consumers have come to expect personalisation as an integral part of their online experience, which is why personalisation has become such an important aspect of website development and ongoing maintenance.
But while personalisation shouldn’t be treated as an afterthought, it’s also not something you can always attempt as part of your site’s initial launch, when you don’t have the required user and behavioural data. However, that doesn’t mean you shouldn’t plan ahead for it. Instead, build your site to accommodate personalisation, even if the implementation will come later.
Generally speaking, there are two approaches organisations can take when it comes to personalisation: again, there’s one where you use an external system (like Google Optimize or Salesforce Experience Cloud) to handle personalisation or one where personalisation is handled within the system as an in-built internal mechanism.
The following are a few examples of each approach in action:
Internal Personalisation
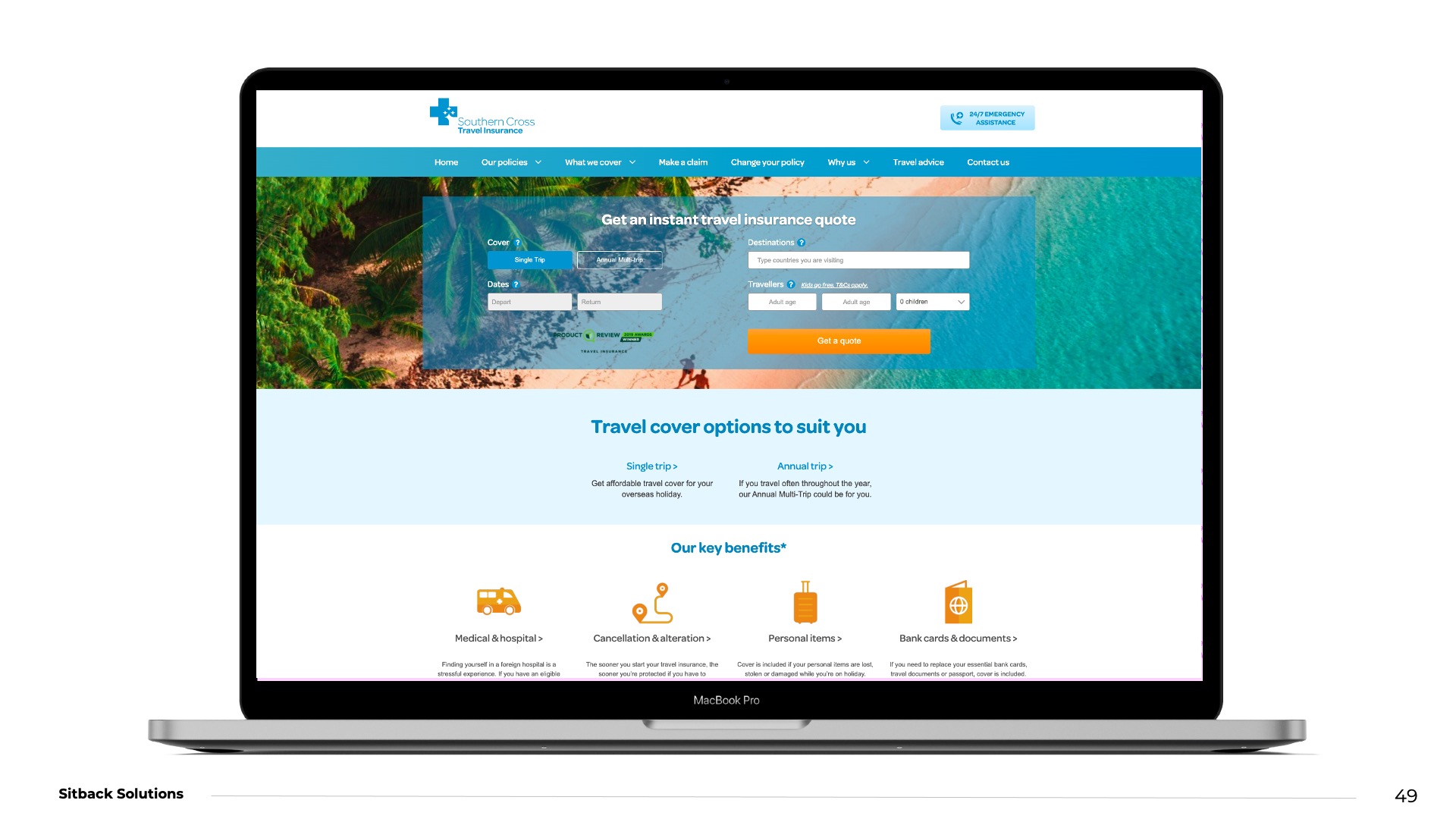
One example of personalisation through the use of internal tools is the Southern Cross Travel Insurance website. In this case, internal tools implemented by Sitback make it possible for the site’s banner image and other information to be changed dynamically, based on the user’s detected IP address. Because the company operates in Australia and New Zealand, the site can automatically display three banners: one for AU, one for NZ, and one for visitors outside of Australia or New Zealand.
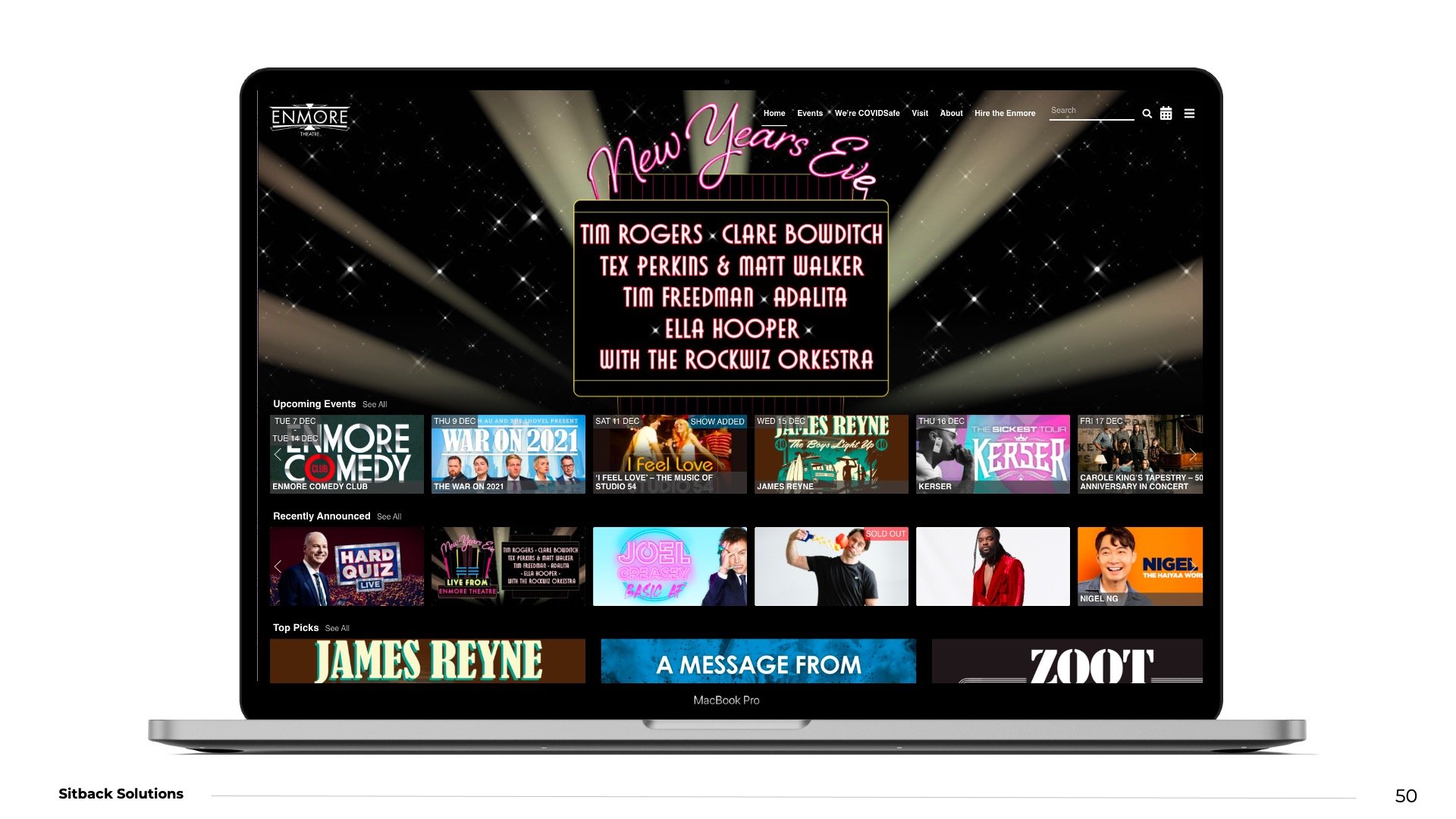
Personalisation can also adapt content based on personal preferences. For example, another Sitback client, Century Venues — who run some of the biggest live music and comedy venues in Sydney — display a list of events on their website.
Because of the way their site stores data in-session, their content can dynamically update to prioritise the events individual visitors are most likely to be interested in, based on the events they interacted with most in previous sessions.
External Personalisation
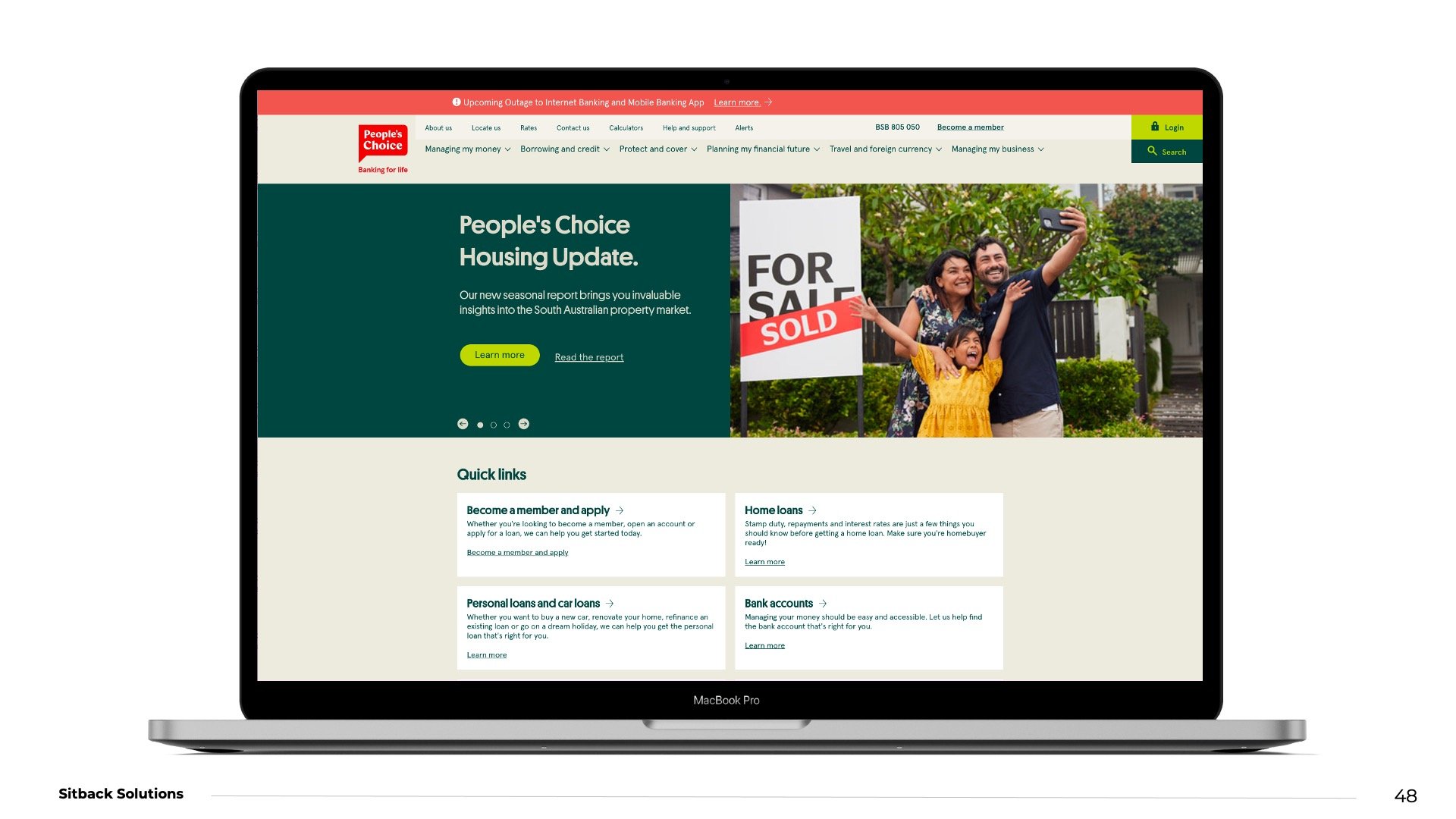
A good example of external personalisation is the People’s Choice website Sitback recently built. In this case, personalisation is handled by an external system through Salesforce. With this system in place, People’s Choice editors are able to manage the personalisation via the external system, with content changes appearing based on users’ on-site behaviour.
Personalisation in Drupal
Finally, when it comes to personalisation within Drupal, it’s a good idea to start small with the Smart Content Module, which enables anonymous and real-time web personalisation within Drupal 8 and 9 (and which comes included with the Smart Content Blocks and the Smart Content Browser modules).
Once implemented, site admins can use the Smart Control Module to display different content for different user roles, based on browser conditions. For instance, the module can be used to display different content to a returning user or to optimise content for a mobile user, using conditions that are evaluated on the client-side to decide what to show or hide.
As your requirements grow, however, you may find that you need to implement a proper, in-depth approach to personalisation. Acquia Personalization would be a good option here, as it integrates easily with Drupal and enables true personalisation on a one-to-one level.
If you’re interested in learning more about personalisation and the options available to you regardless of your level of personalisation maturity, check out our webinar on “Overcoming personalisation paralysis: start small, learn fast”.
Ultimately, whatever approach you decide to take to Drupal personalisation, the right partner can make all the difference when it comes to selecting and implementing the options that’ll have the biggest impact on your visitors’ on-site experience. For support understanding the full breadth of Drupal personalisation possibilities — or for assistance with Drupal performance, accessibility, or security — reach out to Sitback’s expert team.